Streamlining Your Security Documentation
SecBoost helps Australian organisations meet the requirements of the Information Security Manual (ISM) by streamlining the creation, maintenance and compliance of policy, plan and procedure documents.
Designed to support PROTECTED-level IRAP assessments, SecBoost reduces the manual workload involved in interpreting controls, mapping them to business operations, and generating tailored, cross-referenced documentation.
SecBoost automates your System Security Plan Annex, policy generation and control tracking, enabling you to meet ISM obligations with minimal overhead.
- ISM controls
- 1,115
- Documentation suite
- 20+
- Outcome
- Faster
- Estimated savings
- $38k
ISM Mar 2026 Controls
Tailored plans, policies & standards
Audits and assessor workflows
Annual cost savings
Features
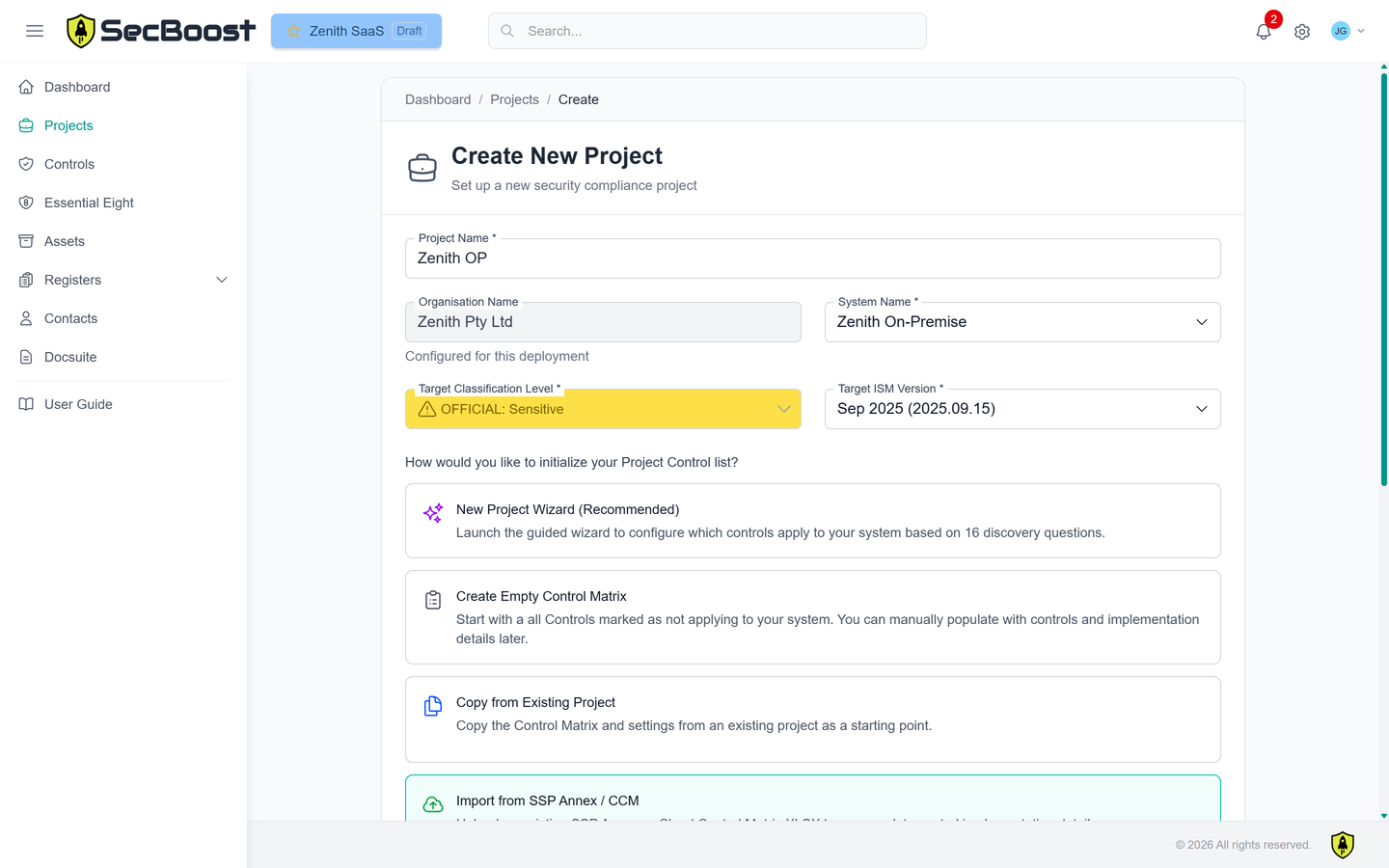
Define your compliance scope
Start with your classification level and ISM version. Use our New Project Wizard to initialise your System Security Plan (SSP) Annex and Control Matrix. Further tailor this to select which controls apply to your business. Record your implementation of those controls within the system.
Create your policies, plans & procedures
SecBoost auto-generates 20+ aligned documents, customised with your branding. Each is pre-filled, and control-mapped to the ISM. Optionally include details about control implementation and assessments live, inside your documentation suite.
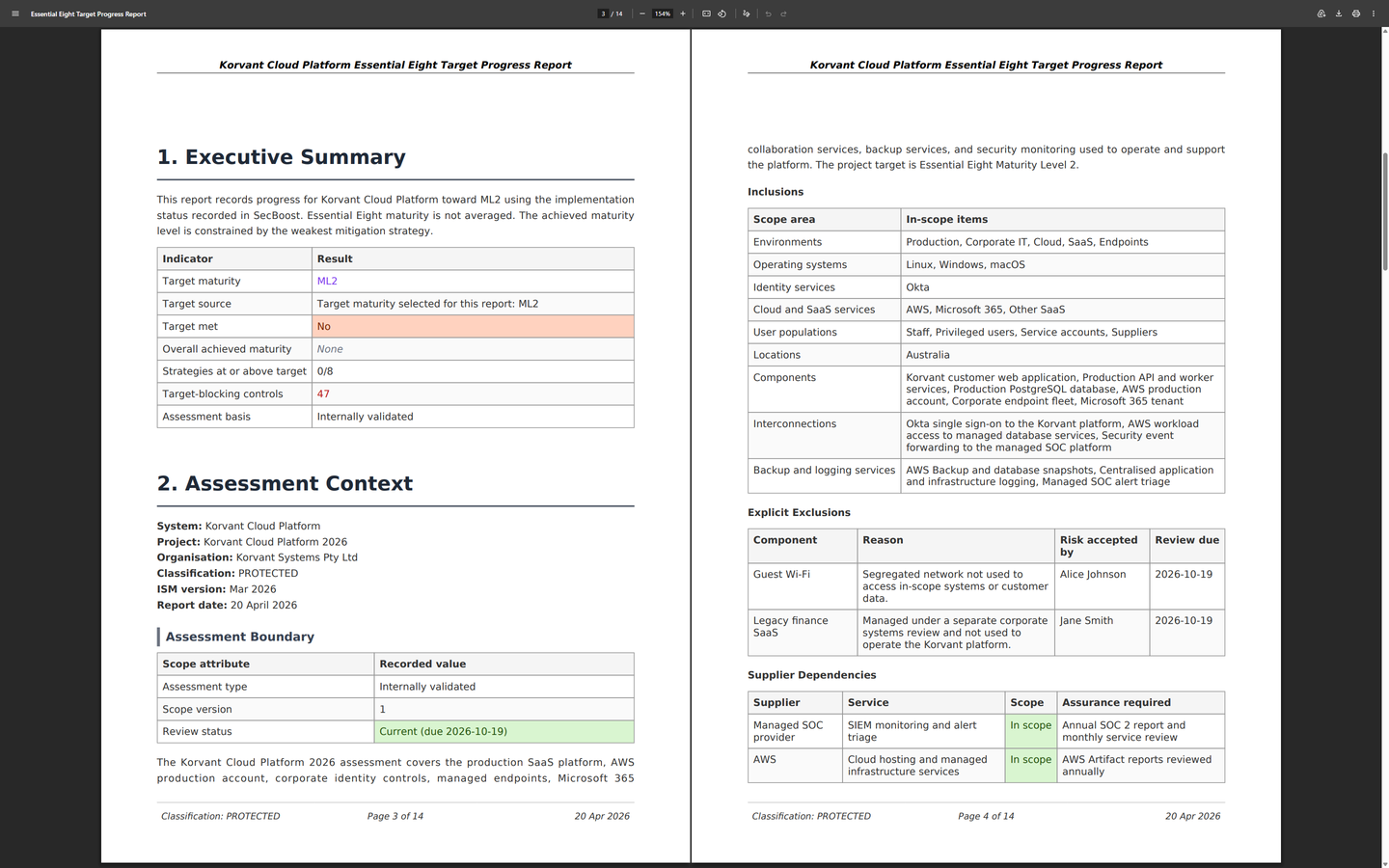
Essential Eight reporting pack
SecBoost now generates Essential Eight target progress and portfolio executive reports, giving teams a clearer view of target maturity achievement, blockers, alternate controls, no-visibility gaps, and residual risk across one system or an organisation-wide portfolio.
March 2026 ISM coverage
SecBoost now supports the March 2026 ISM release across your project setup, SSP Annex, generated matrices, and generated documentation. That includes the updated cyber security principles plus new and amended controls covering areas such as executive AI accountability, cyber supply chain security, cryptographic agility, operational technology isolation, enterprise mobility, and secure AI application development.
AI Security compliance coverage
The December 2025 ISM introduced 14 new AI security controls (ISM-2074, ISM-2082 to ISM-2094), covering AI usage policy, model risk, data poisoning, and output validation. SecBoost maps all of these to your Control Matrix and generates a dedicated Artificial Intelligence Security Policy tailored to your organisation - so you're covered out of the box.
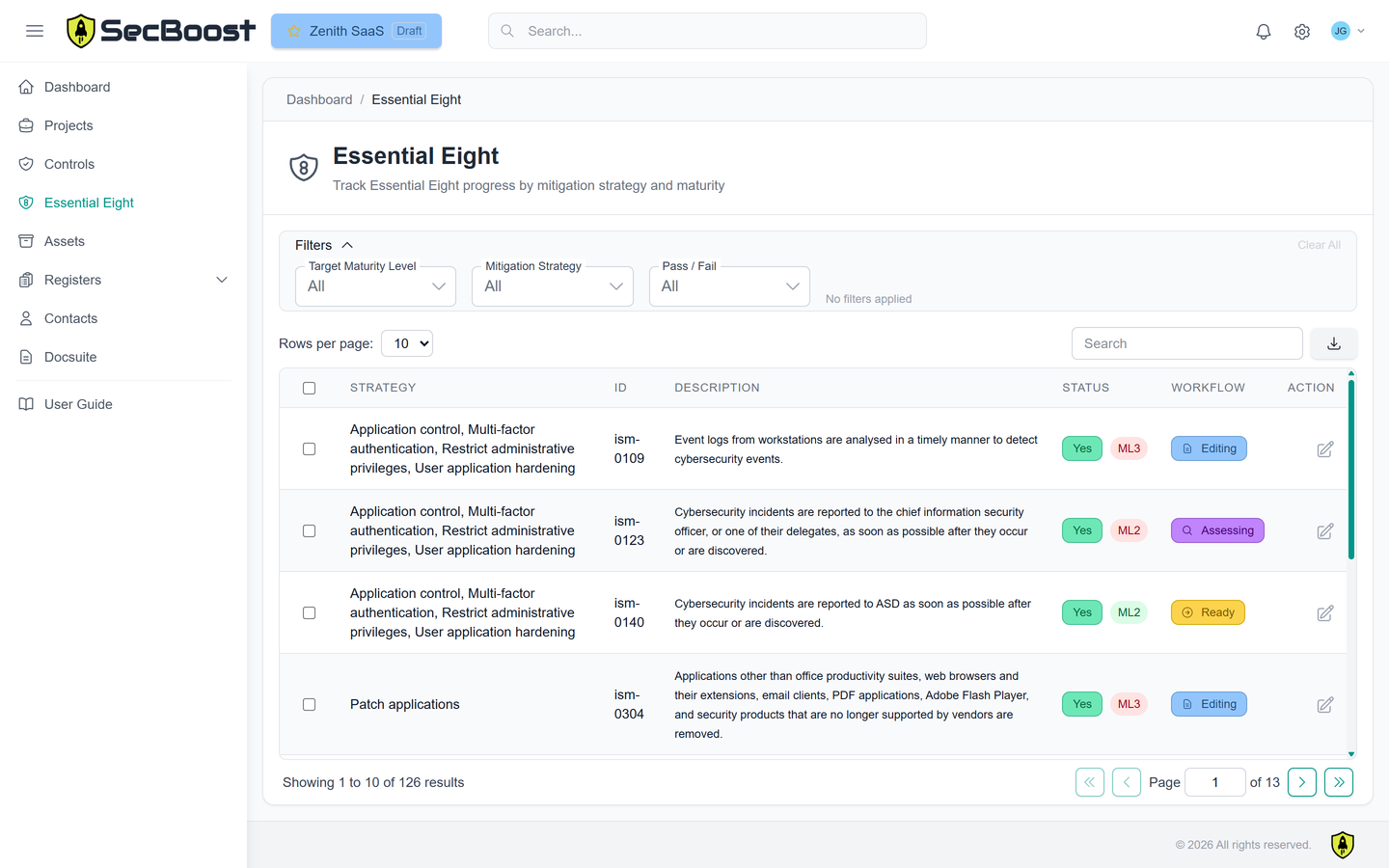
Essential Eight compliance tracking
The Essential Eight provides a baseline of eight mitigation strategies, with a maturity model published by ASD that maps maturity requirements to ISM controls.
SecBoost helps you track maturity progress, capture evidence, and keep your documentation aligned with your selected ISM version - so the same work supports operational uplift, compliance reporting, and executive portfolio reporting.
DISP Cyber Security
Defence states that all Defence Industry Security Program (DISP) members are required to achieve and maintain compliance with the full Essential Eight at Maturity Level 2 (ML2).
DISP members complete the Essential Eight Cyber Security Questionnaire (CSQ) as part of the Annual Security Report (ASR) in the DISP Member Portal, and the CSQ is aligned with Essential Eight Maturity Level 2.
SecBoost helps you answer these questions, guides your security uplift, and gives you a single place to track Essential Eight maturity, implementation evidence, and the supporting documentation needed for ongoing assurance. Learn more on Defence’s DISP Cyber Assurance page.
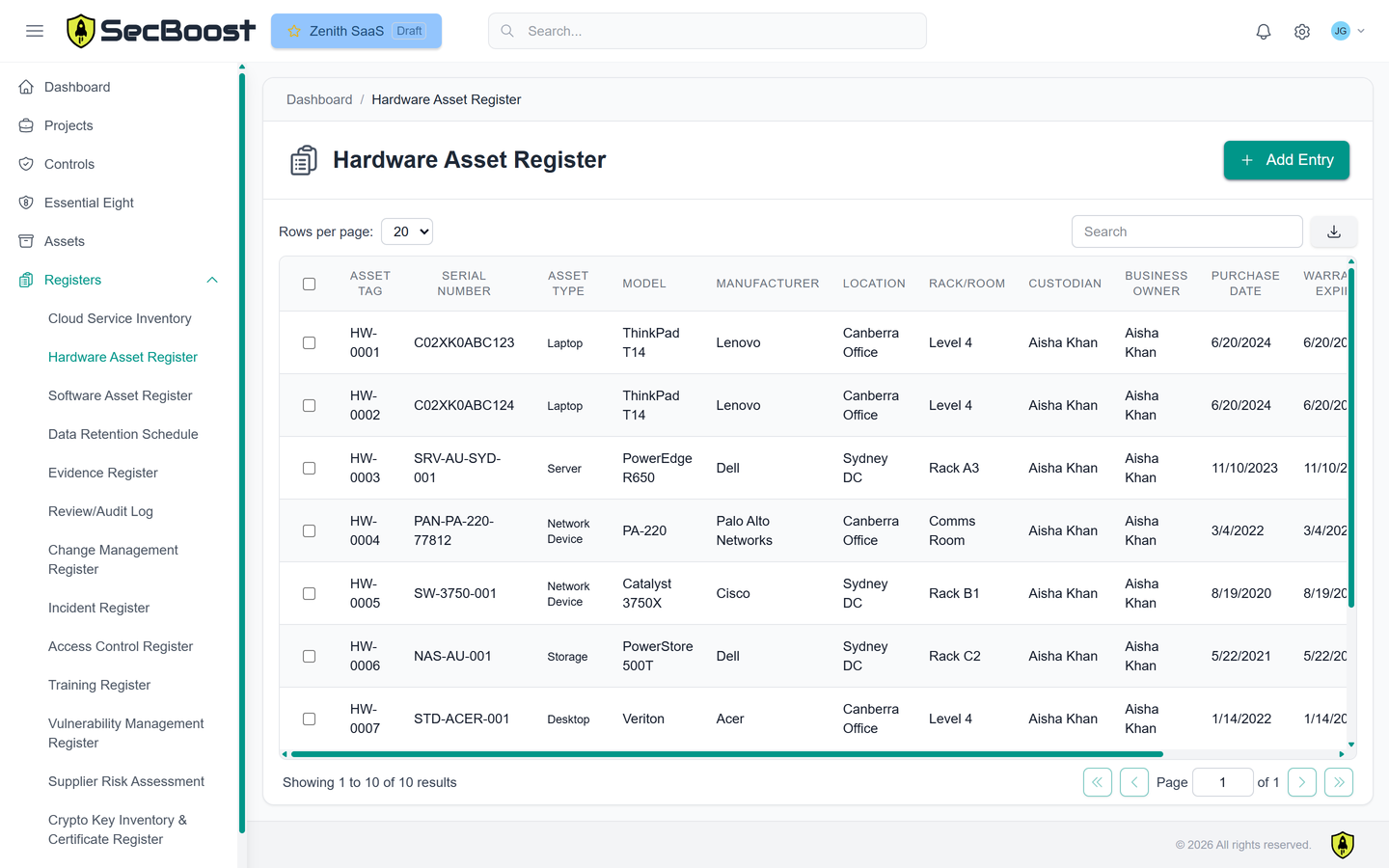
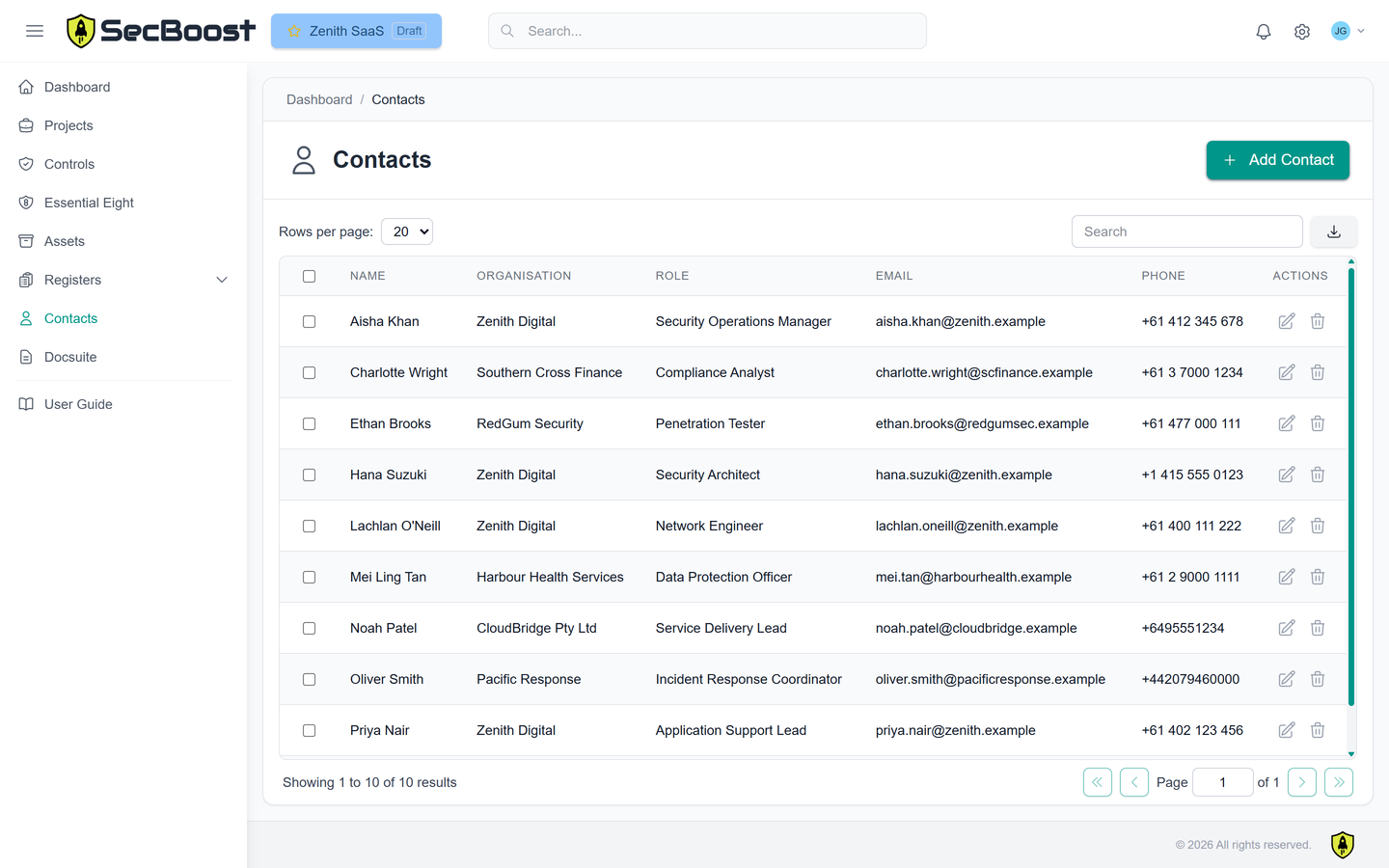
Registers & contacts
Keep the supporting records up-to-date alongside your controls and documentation suite.
Pricing Plans
Choose the plan that best suits your organisation's needs. All plans include ISM March 2026 compliance support.
Starter
$7k/year + GST
Capture control implementation and produce documentation
- ✓ Document generation (20+ plans, policies and procedures tailored to your ISM)
- ✓ Full ISM support (updated Mar 2026)
- ✓ Wizard-based project creation (with 16 discovery questions)
- ✓ SSP Annex and Control Matrix Excel import
- ✓ Basic control workflow (New, Editing, Ready for Assessment)
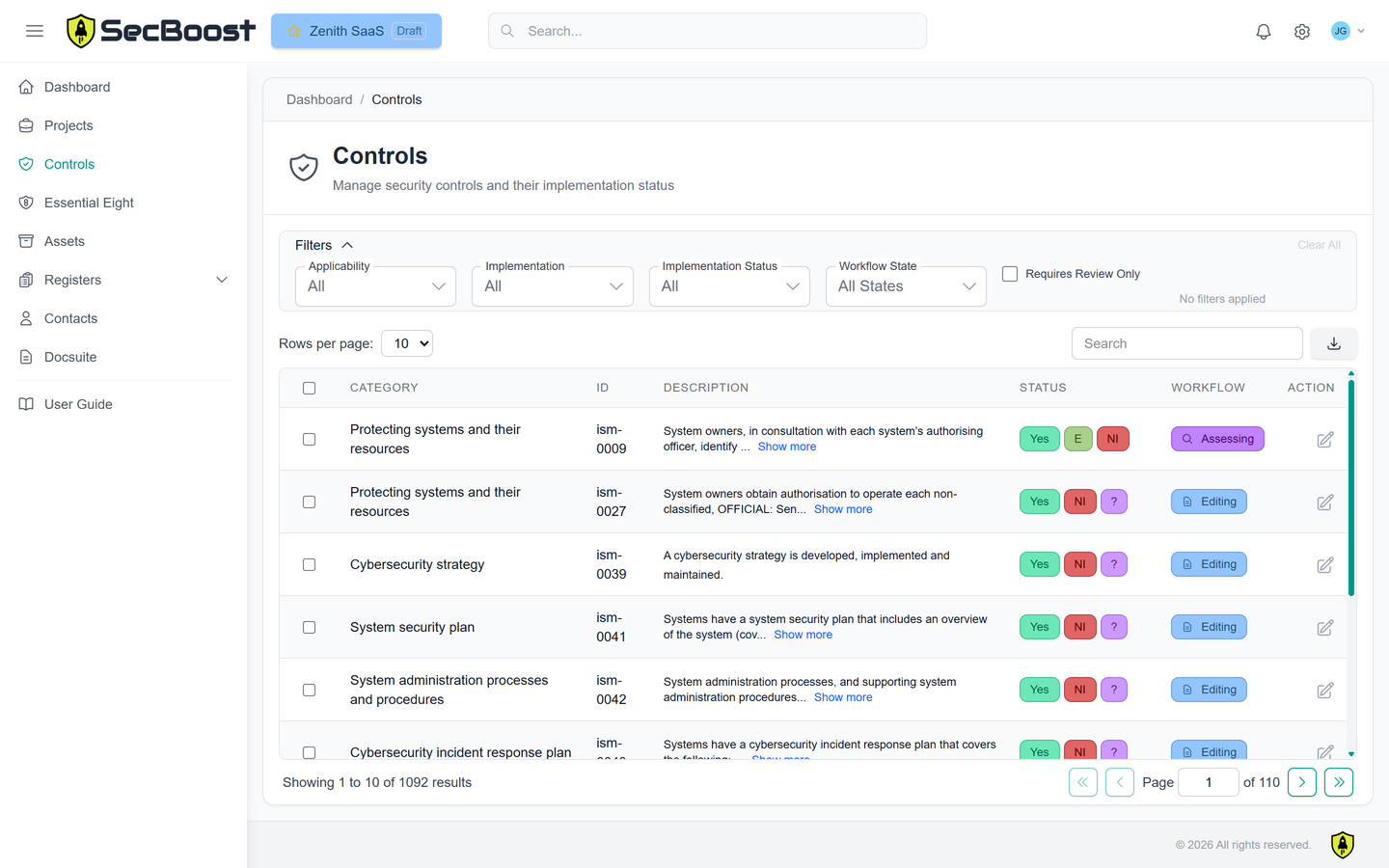
- ✓ Dashboard and filterable/sortable control list
- ✓ Essential 8: dashboard, control index and report document
- ✓ Drag-and-drop evidence attachments for controls New
- ✓ Asset library (store logos, diagrams, contact lists)
- ✓ Classifications: Non-classified, OFFICIAL Sensitive, and PROTECTED
- ✓ Passkey and TOTP MFA
- ✓ Multiple projects for a single assessed system
- ✓ 5 users maximum
- ✓ 5 GB storage
- ✓ Business hours email support
- ✓ 1 hour onboarding support and training
- ✓ Single-tenant AWS PROTECTED environment
Standard
Most Popular$12k/year + GST
Full workflow with assessor collaboration and approval steps
- ✓ Everything in Starter, plus:
- ✓ Full control workflow (includes approval and assessment steps)
- ✓ Customisable roles and permissions
- ✓ Registers (10+ including Hardware, Training, Contacts, etc.)
- ✓ Up to 2 assessed systems, each with multiple projects
- ✓ 20 users maximum
- ✓ 20 GB storage
- ✓ Business hours priority phone support
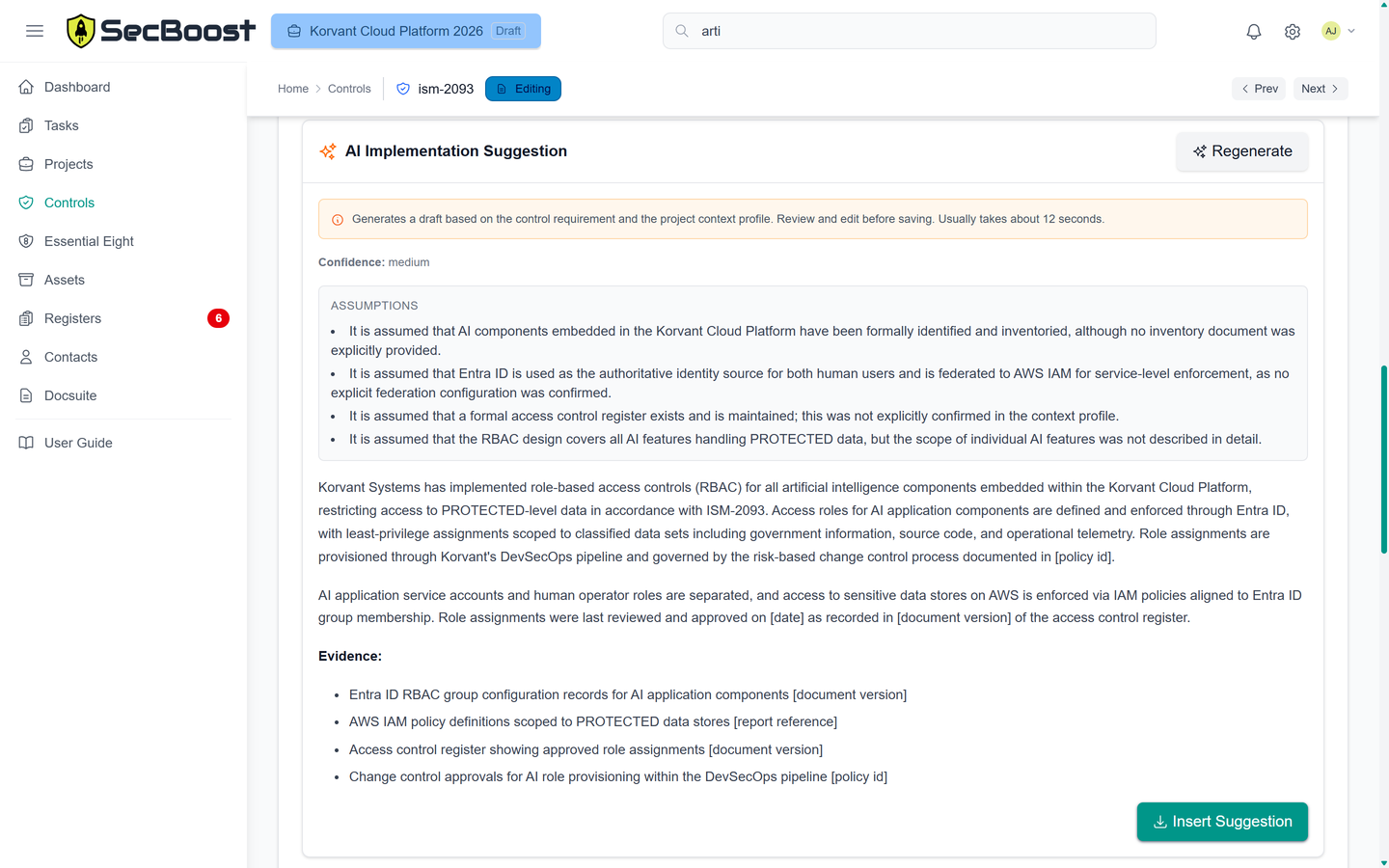
- ✓ AI-generated implementation suggestions matching your system's profile New
- ✓ JIRA integration (optional) New
- ✓ Single-tenant AWS PROTECTED environment
Enterprise
Contact us
Larger scale organisations that host multiple services or perform third party assessments
- ✓ Everything in Standard, plus:
- ✓ Custom domain (e.g., secboost.yourorg.gov.au)
- ✓ Multiple organisations, assessed systems, and projects
- ✓ Task management with reminders, escalation, and reporting
- ✓ Group users into Teams and assign tasks to specific teams or users
- ✓ Custom workflow gates requiring specific fields or tasks
- ✓ SSO with JIT provisioning for roles and Teams
- ✓ On-premises deployment option
- ✓ Classifications: SECRET and TOP SECRET
- ✓ Unlimited users
- ✓ Configurable storage
- ✓ Extended support
- ✓ Custom training sessions
- ✓ Quarterly compliance reviews
- ✓ Annual penetration test reporting
Ready to Get Started?
Simplify your security documentation and meet your ISM compliance obligations.
Get startedFrequently Asked Questions
How does SecBoost automate tasks?
SecBoost maps ISM controls to your chosen scope, generates tailored documentation, and keeps everything aligned with your SSP and the ISM — all with minimal manual effort.
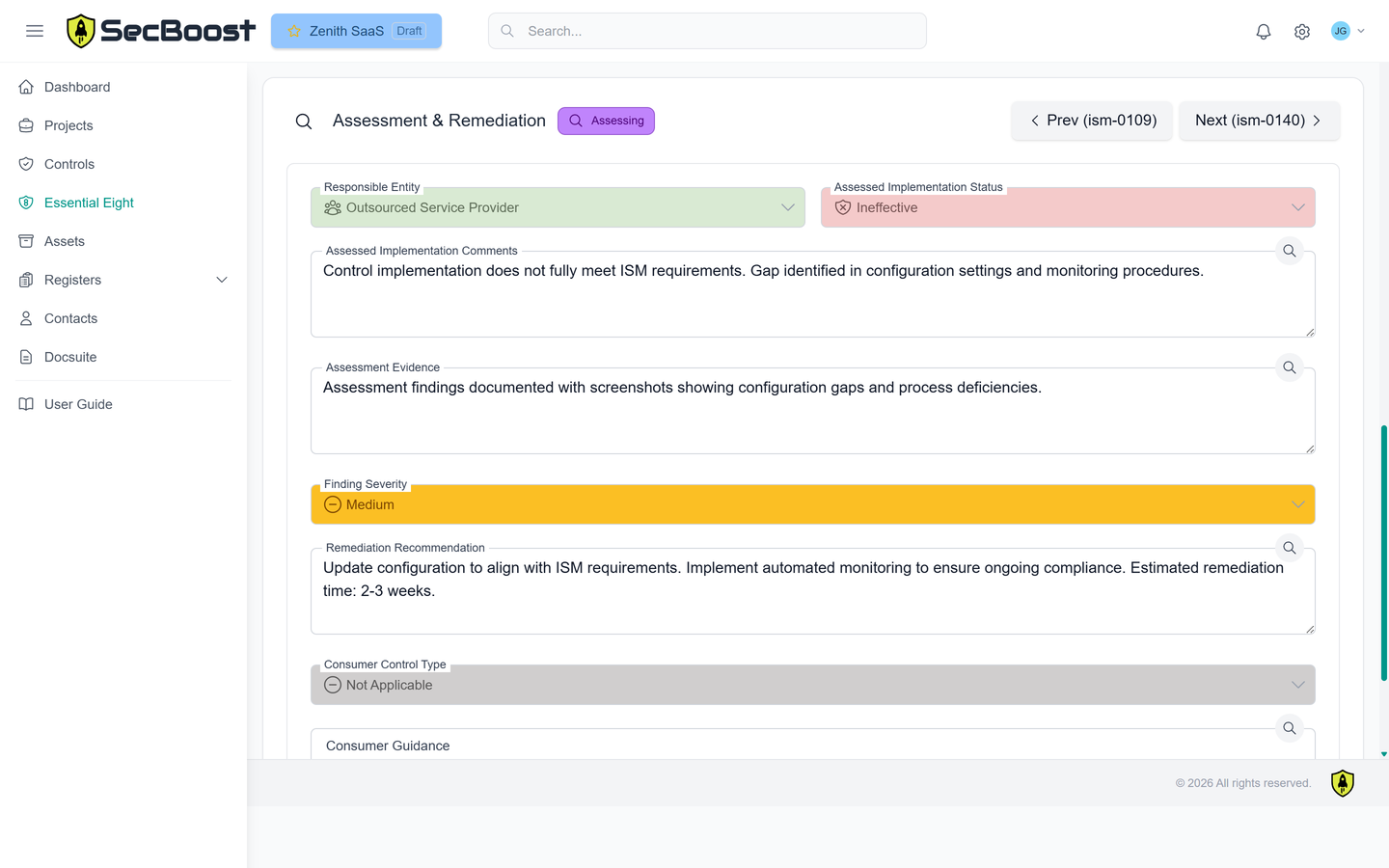
When it comes time to be IRAP assessed, SecBoost provides a single source of truth for the auditor, letting assessors drill into control implementations and track assessments directly in the platform.
What is a System Security Plan (SSP)?
The SSP is the formal document providing a complete overview of your cloud service — its purpose, architecture, data flows, security authorisations, and operational environment. It's the primary document an IRAP assessor uses to understand what they are assessing.
SecBoost assists in the creation of your SSP and SSP Annex, tracking compliance in a single, easy-to-manage platform.
What is the SSP Annex?
Similar to a Statement of Applicability, the SSP Annex is the official spreadsheet that defines the assessment boundary — the clear scope of what an assessor will review, based on the ISM. Each row represents one ISM control, with space to nominate responsibility, state implementation effectiveness, and describe your implementation.
SecBoost supports import and export of the ACSC's SSP Annex spreadsheet template.
Who benefits from using SecBoost?
How does collaboration work?
Is documentation always up-to-date?
Who is SecBoost?
Machine-readable compliance: OSCAL export
SecBoost generates a complete OSCAL 1.1.2-compliant export of your System Security Plan and Assessment Results - in the machine-readable JSON format defined by NIST.
The SSP export maps every applicable ISM control to a structured
implemented-requirement,
capturing your implementation narrative, workflow state, applicability, and responsibility. The
Assessment Results export captures assessor observations, finding severity, and remediation
recommendations for each control - including the date each control was assessed.
OSCAL exports are ready for direct import into OSCAL-aware tooling, including AWS Audit Manager and NIST validation tools, and are schema-validated against the NIST OSCAL 1.1.2 specification before download.
What's included
- NIST OSCAL 1.1.2 - System Security Plan (SSP) and Assessment Results (AR)
- Per-control observations with assessment outcome, date assessed, and finding severity
- Adverse control findings with remediation recommendations
- SecBoost-namespaced properties preserve full workflow state in the export
- Schema-validated before download
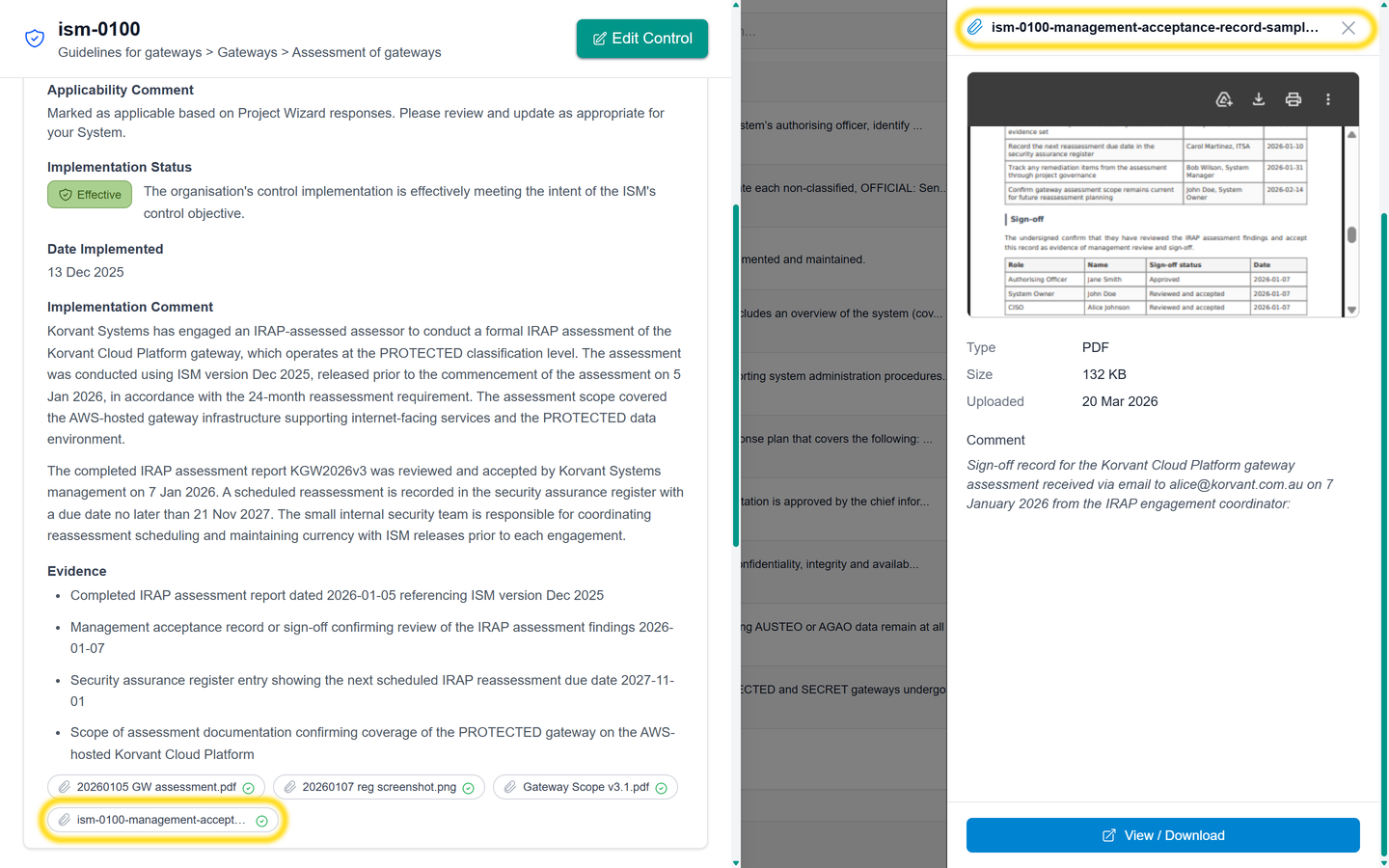
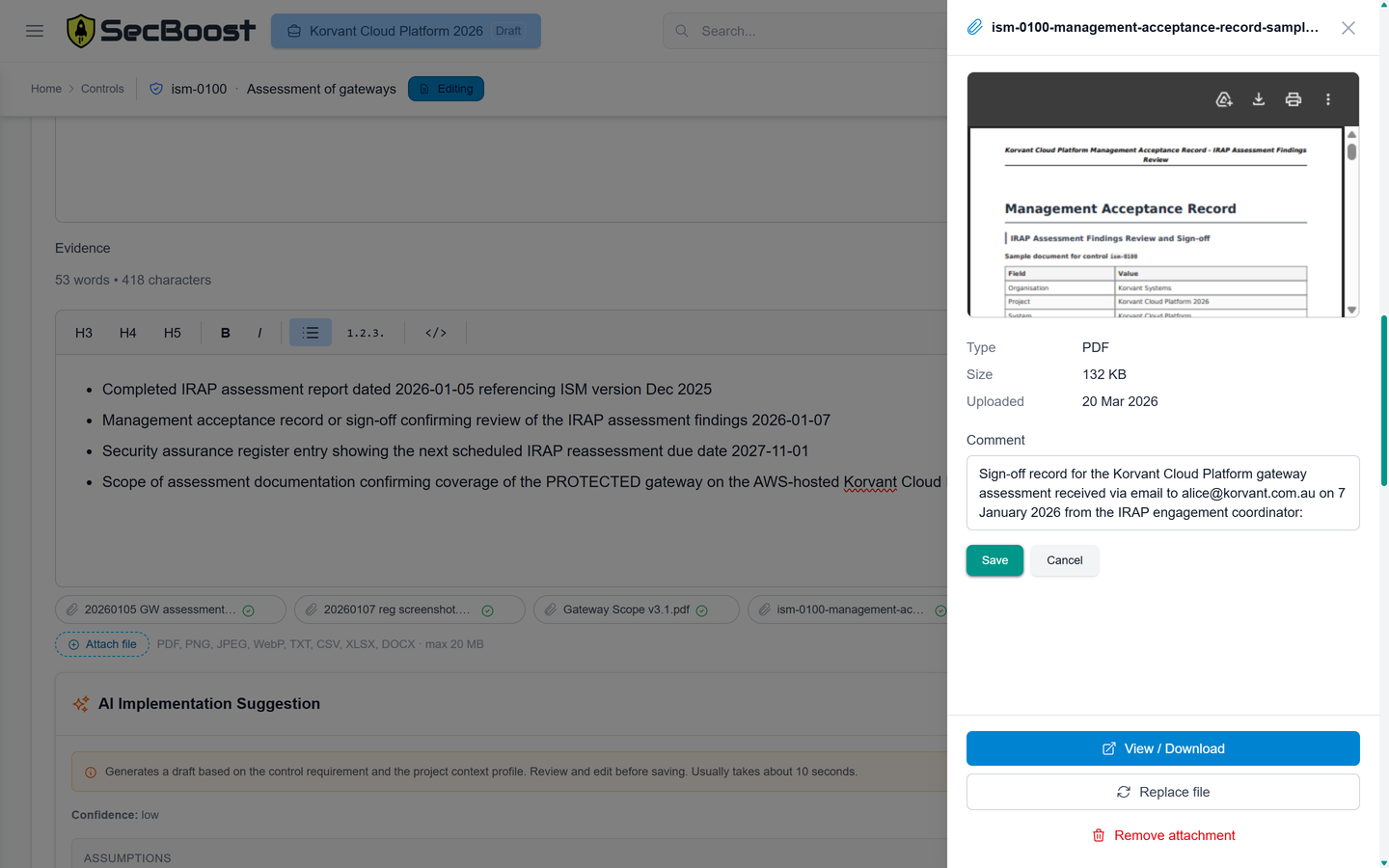
Drag-and-drop evidence attachments
SecBoost now lets you attach implementation evidence directly to individual controls using simple drag-and-drop upload. Add screenshots, PDFs, exports and other supporting records exactly where your team and IRAP assessor need them, with uploaded evidence files automatically virus scanned during processing.
Evidence sits alongside the control implementation, comments and assessment history, keeping each control easier to review and maintain over time.
This keeps evidence organised, reduces back-and-forth during assessment, and gives you a clearer audit trail as your system and documentation evolve.
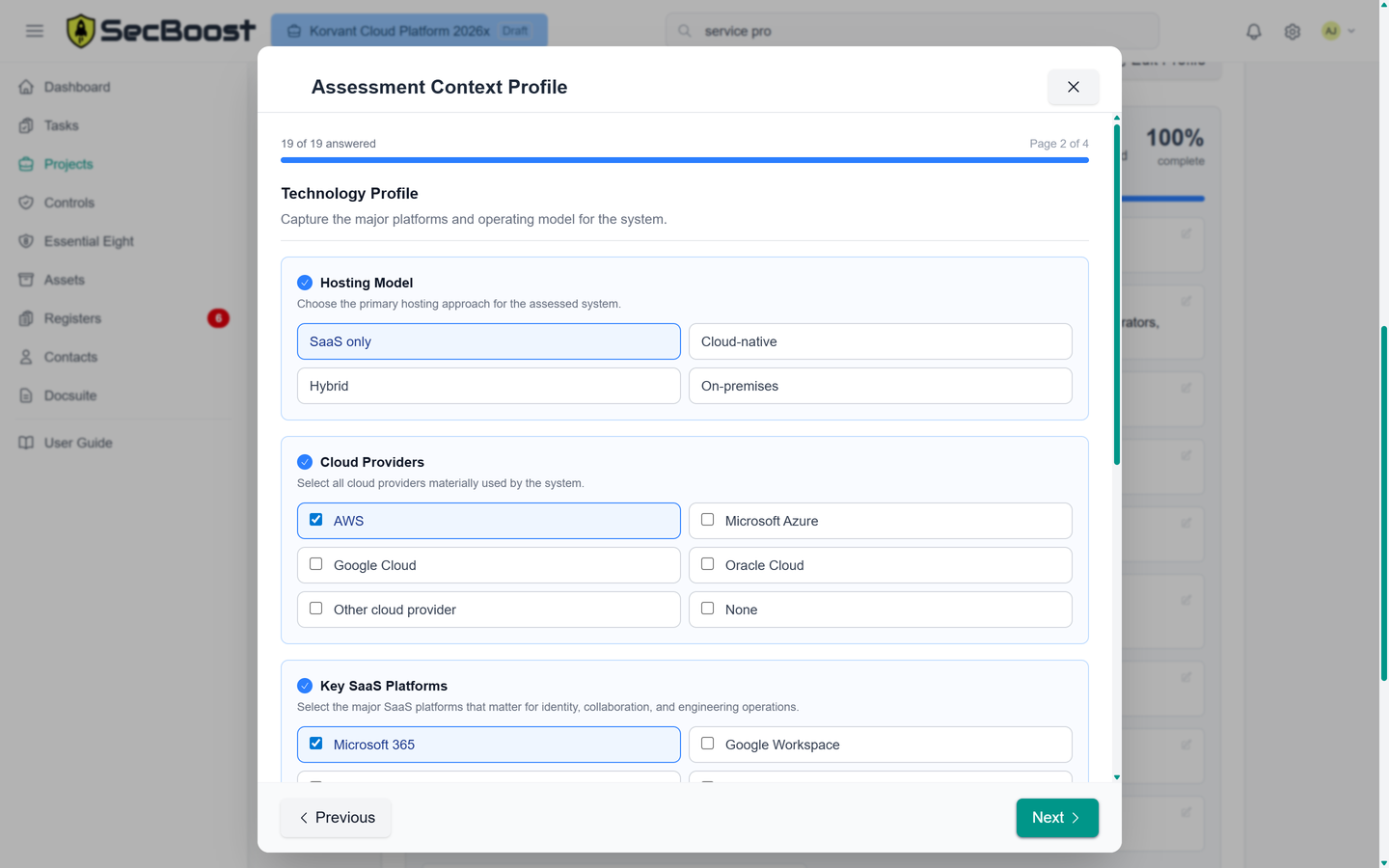
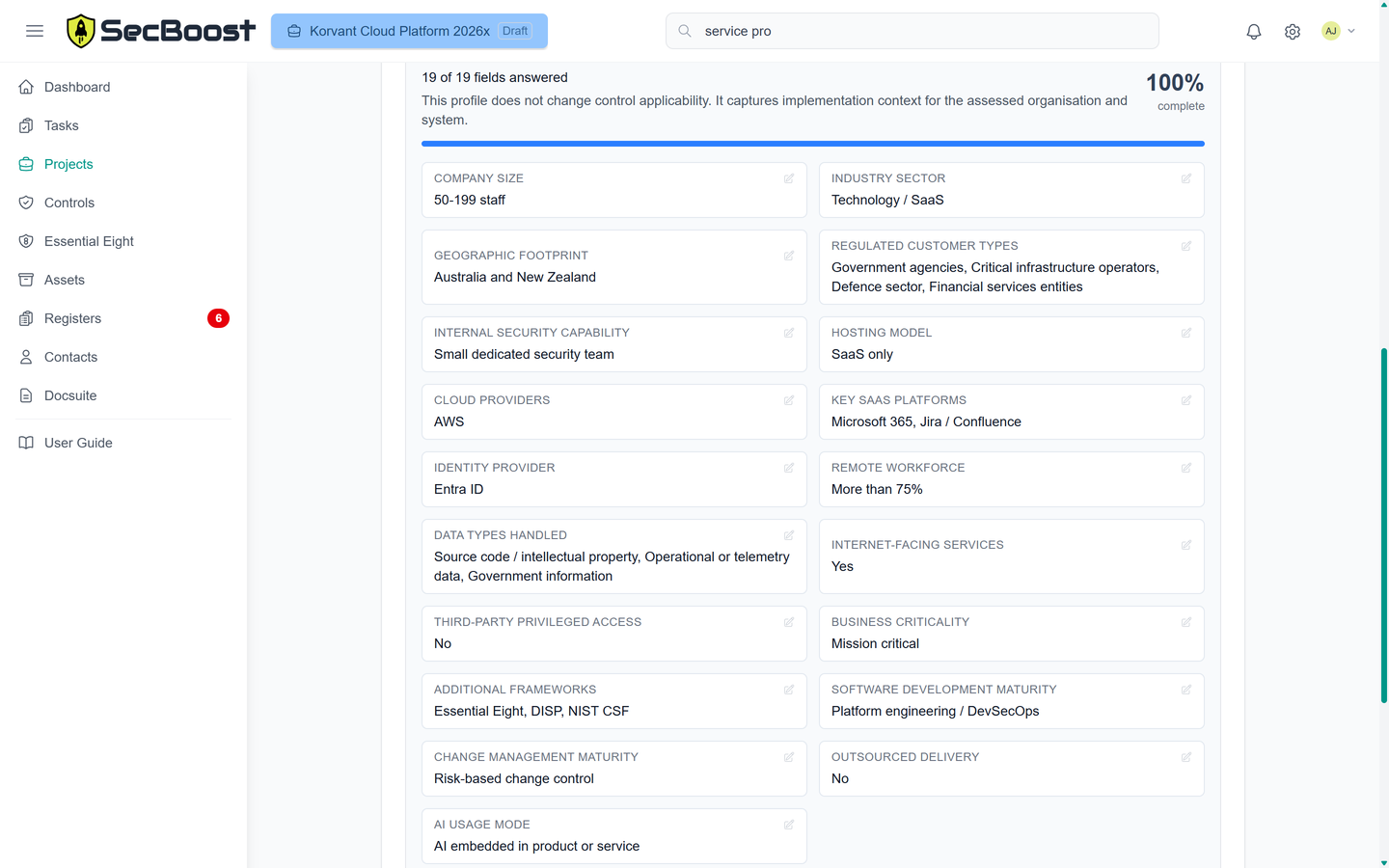
Context-aware IRAP guidance
SecBoost now asks a structured set of project context questions during setup, covering your organisation, system architecture, cloud platforms, data profile, and delivery model.
That context is then used to power an AI control implementation helper for controls in editing, generating concise implementation suggestions aligned to the ISM control requirements and your project's actual environment - so you get more relevant guidance, faster.
AI suggestions are generated using an Australian-hosted service that has undergone an IRAP assessment at the PROTECTED level.
Documentation Suite
The SecBoost system will generate the following ISM compliant documents matching your tailored control applicability and implementations, ISM version, and classification level.
Policies
- Access Control Policy
- Artificial Intelligence Security PolicyNew
- Asset Management Policy
- Backup & Recovery Policy
- Change Management Policy & Procedure
- Cloud Security Policy
- Cryptographic Controls Policy
- Data Classification and Handling Policy
- Email and Communications Policy
- Endpoint Protection Policy
- Information Security Policy
- Interconnection Security Policy
- Logging & Monitoring Policy
- Physical Security Policy
- Secure Development Policy
- Supplier Security Management Policy
Registers
Managed and filled in within the SecBoost system, with full auditing and export to PDF.
- Access Control Register
- Change Management Register
- Cloud Service Inventory
- Crypto Key Inventory & Certificate Register
- Data Retention Schedule
- Evidence Register
- Hardware Asset Register
- Incident Register
- Interconnection Register
- Review/Audit Log
- Software Asset Register
- Supplier Risk Assessment
- Training Register
- Vulnerability Management Register
Plans
- Business Continuity Plan (BCP)
- Disaster Recovery Plan (DRP)
- Incident Response Plan
- Risk Management Plan
- Security Awareness and Training Plan
- Security Review & Audit Plan
- System Security Plan (SSP)
Matrices
Control-aligned matrices for implementation detail, responsibility splits, inherited coverage, and assessor review.
- Cloud Controls Matrix (CCM)
- SSP Annex: ISM Control Implementation Matrix
Standards
- Environment Management Standard
- Network Security Standard
- Platform Security Standard
- System Hardening Standard
- Vulnerability and Patch Management Standard
Reports
Generated reports ready for download, governance review, or submission to assessors.
- Essential Eight Compliance Progress Report
- Essential Eight Portfolio Executive ReportNew
- Essential Eight Target Progress ReportNew
OSCAL Exports
Structured exports ready for import into other tools or submission to assessors.
- OSCAL Assessment Results (AR)New
- OSCAL System Security Plan (SSP)New
Get in touch
Tell us about your system, timeline, and assessment scope. We’ll get back to you shortly.
We work with Australian organisations preparing for IRAP assessments and teams looking to reduce the effort involved in producing ISM-aligned documentation.